|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Mon May 01, 2023 7:07 pm Post subject: FF8 remastered finding instructions problem Posted: Mon May 01, 2023 7:07 pm Post subject: FF8 remastered finding instructions problem |
 |
|
So I tried to find some instructions to make some scripts for the game for learning and practicing purpose. In this case it is the AP received multiplier.
What I usually do is looking for the AP received's address. After that I use CE "find out what write/access to the address" to find the instructions that control the address and manipulate things from there using debugger.
The problem I have with this game is most of the instructions that I found control multiple things (might goes up to thousands addresses)
On the other hand I downloaded a working table and it work just like a champ. Question is how do they were able to find those unique instruction? Is there any special technique?
| Code: |
[ENABLE]
//aobscanmodule(APMultAOB,"FFVIII_EFIGS.dll",66 89 46 32 8B 46 30 8D 0C CD 2C 7F CF 01) // should be unique
aobscanmodule(APMultAOB,FFVIII_EFIGS.dll,0F B7 46 04 50 8B 46 08 8D) // should be unique
registersymbol(APMultAOB)
alloc(newmem,1024,APMultAOB)
label(return)
label(APMult)
registersymbol(APMult)
newmem:
movzx eax,word ptr [esi+04] //original instruction
imul eax,[APMult]
cmp eax,FA
jl originalcode
mov eax,FA
jmp originalcode
originalcode:
push eax
jmp return
APMult:
dq #1
// FFVIII_EFIGS.dll+2F021F
APMultAOB:
jmp newmem
return:
[DISABLE]
APMultAOB:
db 0F B7 46 04 50
unregistersymbol(APMultAOB)
unregistersymbol(APMult)
dealloc(newmem)
|
Last edited by Beginner999 on Mon May 01, 2023 8:27 pm; edited 1 time in total |
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 7:25 pm Post subject: Posted: Mon May 01, 2023 7:25 pm Post subject: |
 |
|
| When you find the correct address and check to see what accesses it, in the new window that pops up, right-click on an empty white space and check to see if found opcodes access any other addresses. If you get a result with a (1) next to it (even after returning to game and back to CE), then you may be able to use that for your injection point.
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Mon May 01, 2023 7:38 pm Post subject: Posted: Mon May 01, 2023 7:38 pm Post subject: |
 |
|
| ++METHOS wrote: | | When you find the correct address and check to see what accesses it, in the new window that pops up, right-click on an empty white space and check to see if found opcodes access any other addresses. If you get a result with a (1) next to it (even after returning to game and back to CE), then you may be able to use that for your injection point. |
I just tried that on exp, gold, draw magic and AP, they all have the same instruction and that instruction is different from the one in the code I attach in earlier 
p/s: also all of the instructions that I found for this game access to multiple addresses, could not find anything that control only 1 address 
Last edited by Beginner999 on Mon May 01, 2023 8:27 pm; edited 1 time in total |
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 7:49 pm Post subject: Posted: Mon May 01, 2023 7:49 pm Post subject: |
 |
|
Make sure that you have found the correct address. If you think that you have it, then compare it to whatever the instruction in the OP is accessing (prior to script activation). Right-click on instruction in memory viewer and check to see what it accesses.
Maybe provide some screenshots so that we have more information to go off of. You may also provide a screenshot of the debugger window so that we can see which instruction(s) are accessing all of those other values (gold, exp etc.).
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Mon May 01, 2023 8:04 pm Post subject: Posted: Mon May 01, 2023 8:04 pm Post subject: |
 |
|
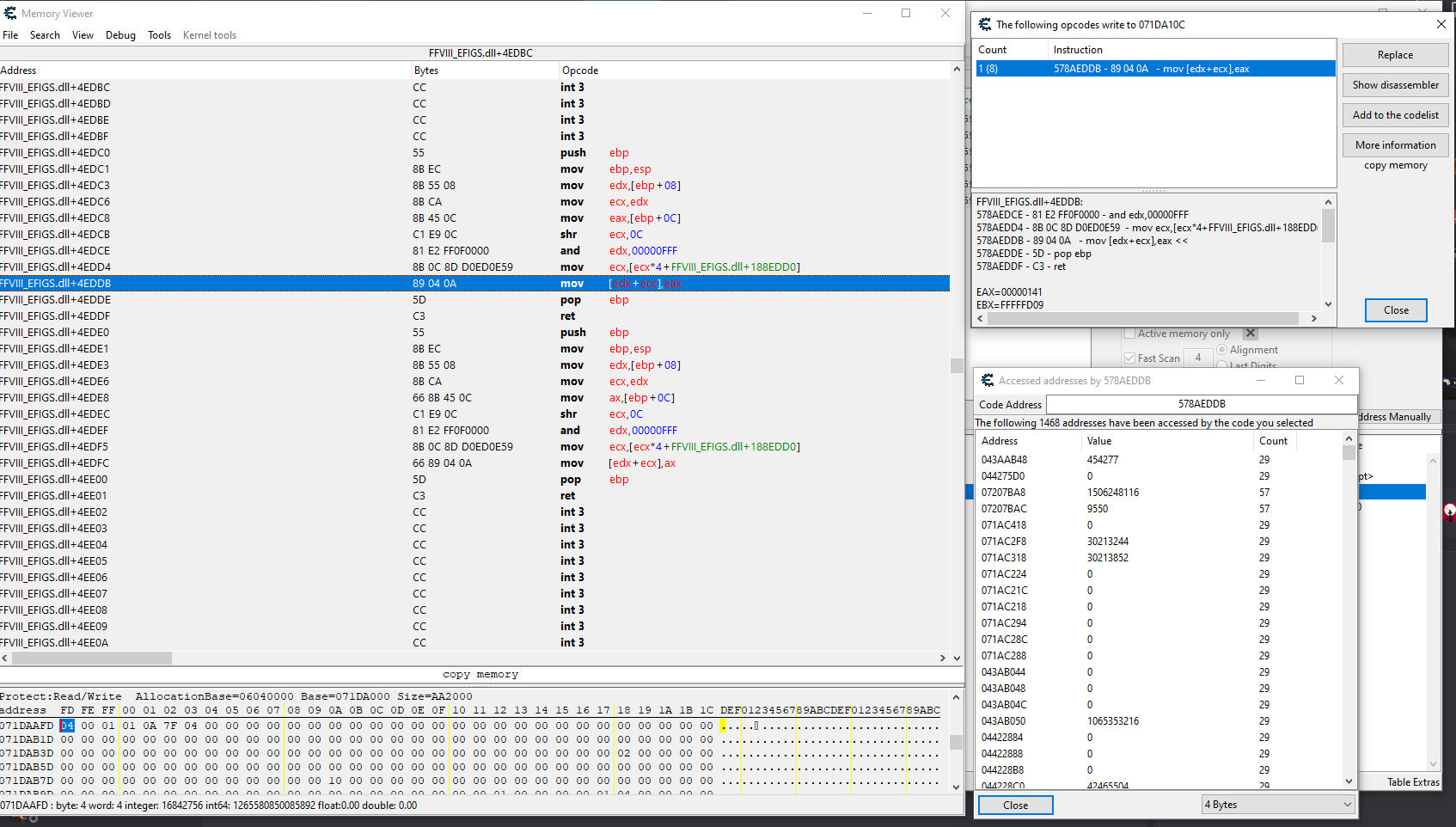
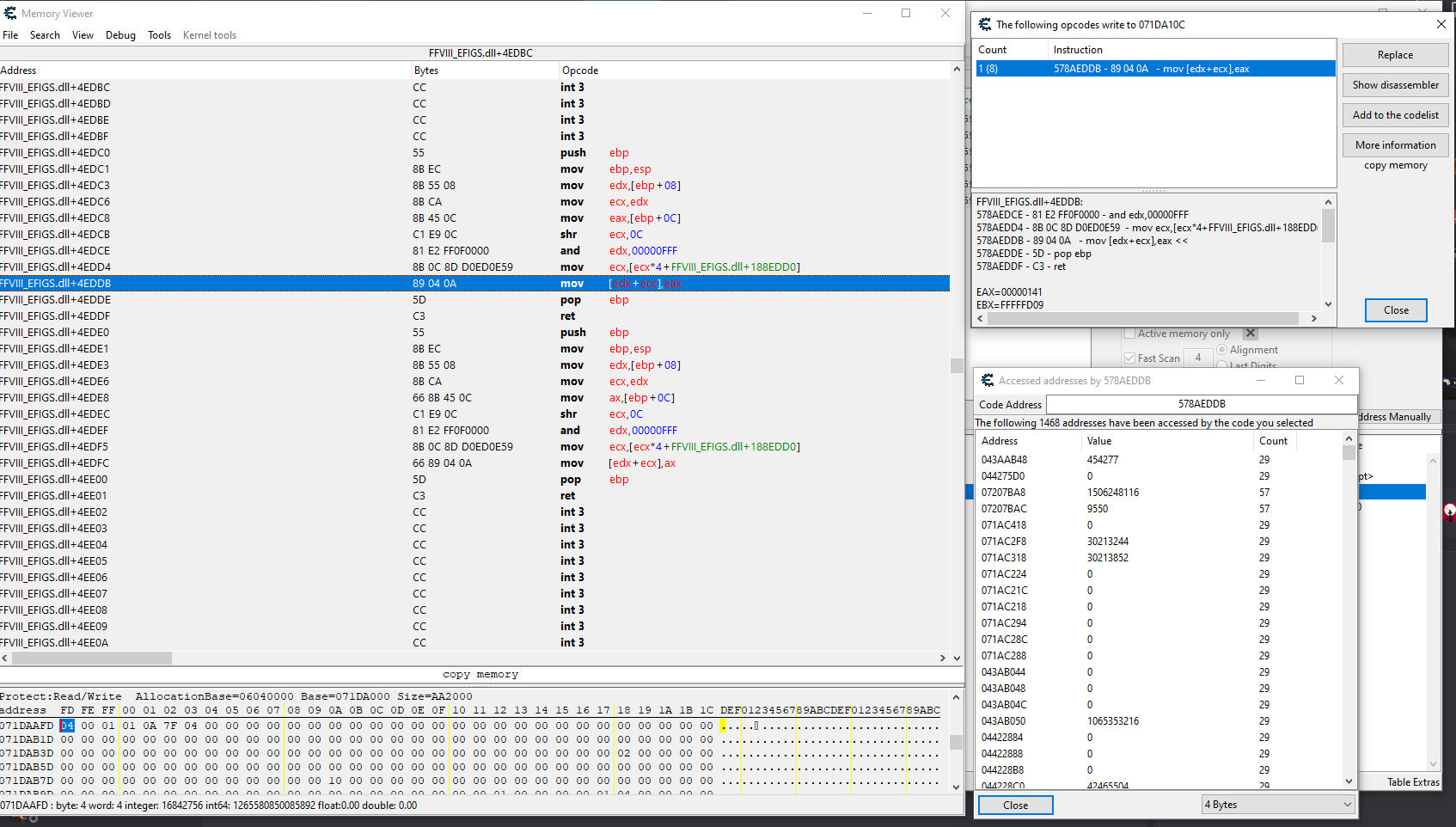
I attached a screenshot of the memory viewer that I found for the Squall EXP. That highlighted line there control all characters Total EXP, AP received, Gil changes, etc.
| Description: |
|
| Filesize: |
134.83 KB |
| Viewed: |
2188 Time(s) |
|
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 8:09 pm Post subject: Posted: Mon May 01, 2023 8:09 pm Post subject: |
 |
|
1. Is the script that you shared in the OP the working script that someone else wrote?
2. If yes, then did you check to see what address(es) that instruction was accessing to see if you have found the correct address?
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Mon May 01, 2023 8:26 pm Post subject: Posted: Mon May 01, 2023 8:26 pm Post subject: |
 |
|
| Quote: | 1. Is the script that you shared in the OP the working script that someone else wrote?
2. If yes, then did you check to see what address(es) that instruction was accessing to see if you have found the correct address? |
1. Yes, that script is someone else script and I have no idea how they could find the address and instructions 
2. I just double check and no, they do not instruct the same address that I found, but at the same time the address that the instruction instruct does not show a solid value and the value does not reflect whatever showing though(value keep changing itself even the count column staying the same). On the other hand the Count column only increase whenever I receive some AP (for the AP script) 
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 8:30 pm Post subject: Posted: Mon May 01, 2023 8:30 pm Post subject: |
 |
|
It sounds like you may not have found the correct address yet.
Is the address that the instruction accesses in close proximity to any of the addresses that you have found (e.g. AP address)?
Also, is the address that the instruction accesses also being accessed by one of the instructions that you found?
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Mon May 01, 2023 8:37 pm Post subject: Posted: Mon May 01, 2023 8:37 pm Post subject: |
 |
|
| ++METHOS wrote: | It sounds like you may not have found the correct address yet.
Is the address that the instruction accesses in close proximity to any of the addresses that you have found (e.g. AP address)?
Also, is the address that the instruction accesses also being accessed by one of the instructions that you found? |
The thing is I was able to control the value and the game work well (I put AP received to 255 and the game let my GF learned the ability). But there may be something else instructing how those value increase or decrease. (and I could not find it  ) )
Also the address that seem to control how AP is gained or multiply is no where close to the one I found.
For the last question it's another no 
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 8:53 pm Post subject: Posted: Mon May 01, 2023 8:53 pm Post subject: |
 |
|
| This is for PC? Do you have a save file?
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon May 01, 2023 9:29 pm Post subject: Posted: Mon May 01, 2023 9:29 pm Post subject: |
 |
|
Looks like your ID is stored in one of the registers (e.g. ecx).
Right-click on an address in your cheat table to see what accesses it (e.g. gold value). In the new window, with the instruction highlighted, check in the lower window pane to see what the value of ecx is (e.g. 764)...or edx.
Now, when you create your script, just set it up to filter out everything that you want to manipulate e.g.:
| Code: | //Target: FFVIII.exe
//Author: ++METHOS
[ENABLE]
{==================== master ====================}
{
// ORIGINAL CODE - INJECTION POINT: FFVIII_EFIGS.dll+15E88A2
FFVIII_EFIGS.dll+15E886D: CC - int 3
FFVIII_EFIGS.dll+15E886E: CC - int 3
FFVIII_EFIGS.dll+15E886F: CC - int 3
FFVIII_EFIGS.dll+15E8870: 8B D1 - mov edx,ecx
FFVIII_EFIGS.dll+15E8872: 81 E1 FF 0F 00 00 - and ecx,00000FFF
FFVIII_EFIGS.dll+15E8878: C1 EA 0C - shr edx,0C
FFVIII_EFIGS.dll+15E887B: 8B 14 95 60 91 68 59 - mov edx,[edx*4+FFVIII_EFIGS.dll+1769160]
FFVIII_EFIGS.dll+15E8882: 8B 04 11 - mov eax,[ecx+edx]
FFVIII_EFIGS.dll+15E8885: 8B 54 11 04 - mov edx,[ecx+edx+04]
FFVIII_EFIGS.dll+15E8889: C3 - ret
FFVIII_EFIGS.dll+15E888A: CC - int 3
FFVIII_EFIGS.dll+15E888B: CC - int 3
FFVIII_EFIGS.dll+15E888C: CC - int 3
FFVIII_EFIGS.dll+15E888D: CC - int 3
FFVIII_EFIGS.dll+15E888E: CC - int 3
FFVIII_EFIGS.dll+15E888F: CC - int 3
FFVIII_EFIGS.dll+15E8890: 8B C1 - mov eax,ecx
FFVIII_EFIGS.dll+15E8892: 81 E1 FF 0F 00 00 - and ecx,00000FFF
FFVIII_EFIGS.dll+15E8898: C1 E8 0C - shr eax,0C
FFVIII_EFIGS.dll+15E889B: 8B 04 85 60 91 68 59 - mov eax,[eax*4+FFVIII_EFIGS.dll+1769160]
// ---------- INJECTING HERE ----------
FFVIII_EFIGS.dll+15E88A2: 8B 04 01 - mov eax,[ecx+eax]
// ---------- DONE INJECTING ----------
FFVIII_EFIGS.dll+15E88A5: C3 - ret
FFVIII_EFIGS.dll+15E88A6: CC - int 3
FFVIII_EFIGS.dll+15E88A7: CC - int 3
FFVIII_EFIGS.dll+15E88A8: CC - int 3
FFVIII_EFIGS.dll+15E88A9: CC - int 3
FFVIII_EFIGS.dll+15E88AA: CC - int 3
FFVIII_EFIGS.dll+15E88AB: CC - int 3
FFVIII_EFIGS.dll+15E88AC: CC - int 3
FFVIII_EFIGS.dll+15E88AD: CC - int 3
FFVIII_EFIGS.dll+15E88AE: CC - int 3
FFVIII_EFIGS.dll+15E88AF: CC - int 3
FFVIII_EFIGS.dll+15E88B0: 8B C1 - mov eax,ecx
FFVIII_EFIGS.dll+15E88B2: 81 E1 FF 0F 00 00 - and ecx,00000FFF
FFVIII_EFIGS.dll+15E88B8: C1 E8 0C - shr eax,0C
FFVIII_EFIGS.dll+15E88BB: 8B 04 85 60 91 68 59 - mov eax,[eax*4+FFVIII_EFIGS.dll+1769160]
FFVIII_EFIGS.dll+15E88C2: 66 8B 04 01 - mov ax,[ecx+eax]
FFVIII_EFIGS.dll+15E88C6: C3 - ret
FFVIII_EFIGS.dll+15E88C7: CC - int 3
FFVIII_EFIGS.dll+15E88C8: CC - int 3
FFVIII_EFIGS.dll+15E88C9: CC - int 3
}
aobscanmodule(aob_master,FFVIII_EFIGS.dll,8B????C3????????????????????8B??81??????????C1????8B)
alloc(newmem_master,1024,FFVIII_EFIGS.dll)
label(return_master)
label(originalcode_master)
label(gold)
label(gold_code)
registersymbol(aob_master)
registersymbol(gold)
newmem_master:
cmp ecx,764
je gold_code
//add other filters here
jmp originalcode_master
gold_code:
push edi
lea edi,[ecx+eax]
mov [gold],edi
pop edi
originalcode_master:
mov eax,[ecx+eax]
ret
int 3
jmp return_master
gold:
dd 0
aob_master:
jmp newmem_master
return_master:
[DISABLE]
dealloc(newmem_master)
aob_master:
db 8B 04 01 C3 CC
unregistersymbol(aob_master)
unregistersymbol(gold) |
You may need to change the AOB signature (and other things) to match your version. Add the script to your table and activate it. Once activated, add an address manually (in the upper-right corner), and check the 'pointer' box. Type gold in the bottom text field and then click okay. Do this for each value that you want to filter out and manipulate. Report back.
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Tue May 02, 2023 6:21 pm Post subject: Posted: Tue May 02, 2023 6:21 pm Post subject: |
 |
|
I could not make the script you provided to work, trying to find the right aobscan but have no luck  . .
Most of my search returned in mov [something],eax or mov [something], ax 
Below is the injection point for my money value
| Code: |
// ORIGINAL CODE - INJECTION POINT: FFVIII_EFIGS.dll+4EDDB
FFVIII_EFIGS.dll+4EDBE: CC - int 3
FFVIII_EFIGS.dll+4EDBF: CC - int 3
FFVIII_EFIGS.dll+4EDC0: 55 - push ebp
FFVIII_EFIGS.dll+4EDC1: 8B EC - mov ebp,esp
FFVIII_EFIGS.dll+4EDC3: 8B 55 08 - mov edx,[ebp+08]
FFVIII_EFIGS.dll+4EDC6: 8B CA - mov ecx,edx
FFVIII_EFIGS.dll+4EDC8: 8B 45 0C - mov eax,[ebp+0C]
FFVIII_EFIGS.dll+4EDCB: C1 E9 0C - shr ecx,0C
FFVIII_EFIGS.dll+4EDCE: 81 E2 FF 0F 00 00 - and edx,00000FFF
FFVIII_EFIGS.dll+4EDD4: 8B 0C 8D D0 ED 7C 59 - mov ecx,[ecx*4+FFVIII_EFIGS.dll+188EDD0]
// ---------- INJECTING HERE ----------
FFVIII_EFIGS.dll+4EDDB: 89 04 0A - mov [edx+ecx],eax
// ---------- DONE INJECTING ----------
FFVIII_EFIGS.dll+4EDDE: 5D - pop ebp
FFVIII_EFIGS.dll+4EDDF: C3 - ret
FFVIII_EFIGS.dll+4EDE0: 55 - push ebp
FFVIII_EFIGS.dll+4EDE1: 8B EC - mov ebp,esp
FFVIII_EFIGS.dll+4EDE3: 8B 55 08 - mov edx,[ebp+08]
FFVIII_EFIGS.dll+4EDE6: 8B CA - mov ecx,edx
FFVIII_EFIGS.dll+4EDE8: 66 8B 45 0C - mov ax,[ebp+0C]
FFVIII_EFIGS.dll+4EDEC: C1 E9 0C - shr ecx,0C
FFVIII_EFIGS.dll+4EDEF: 81 E2 FF 0F 00 00 - and edx,00000FFF
FFVIII_EFIGS.dll+4EDF5: 8B 0C 8D D0 ED 7C 59 - mov ecx,[ecx*4+FFVIII_EFIGS.dll+188EDD0] :? |
Update:
So I tried to use the line above the injecting point
| Code: | | FFVIII_EFIGS.dll+4EDC8: 8B 45 0C - mov eax,[ebp+0C] |
The pointer seem to jump between few addresses and the values in these addresses constantly changing 
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Tue May 02, 2023 7:14 pm Post subject: Posted: Tue May 02, 2023 7:14 pm Post subject: |
 |
|
| Don't even worry about my injection point. You already have found it (it's the instruction that accesses gold). Just create a script using your injection point and follow the instructions provided and you should be good. You may need to choose a different register to compare, but other than that, it should be similar.
|
|
| Back to top |
|
 |
Beginner999
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 27 Jul 2018
Posts: 21
|
 Posted: Tue May 02, 2023 7:37 pm Post subject: Posted: Tue May 02, 2023 7:37 pm Post subject: |
 |
|
| ++METHOS wrote: | | Don't even worry about my injection point. You already have found it (it's the instruction that accesses gold). Just create a script using your injection point and follow the instructions provided and you should be good. You may need to choose a different register to compare, but other than that, it should be similar. |
I was so blind, I find the opcodes that write instead of access. With that fixed I got the similar opcodes like your script and here's the result:
I was able to find a pointer with the script,
| Code: |
07027D78 //old gold address
06F03D78 //current gold address
06E4FD78 //current pointer point to this address
|
Seem like the pointer point to the base address of gold  . Also sometimes the pointer itself jump to the current gold address too, I started to feeling something positive here . Also sometimes the pointer itself jump to the current gold address too, I started to feeling something positive here 
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|