|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
marco0999
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 28 Jun 2020
Posts: 29
Location: Italy
|
 Posted: Sat Jun 25, 2022 7:01 am Post subject: Apply a Patch to a Game with IDA Posted: Sat Jun 25, 2022 7:01 am Post subject: Apply a Patch to a Game with IDA |
 |
|
I have created a c++ wrapped version of "winmm.dll" that use hook some games.
To do it I use detours and until now I have succefully hook 32 and 64 bit games.
Unfortunatenly I have found some issue to hook a game:
After hook the game start normally but after 15 second the game crash a show a messagebox "Signature Verification of executible failed".
If I remove this line on my dll:
| Code: |
DetourAttach(&(LPVOID&)AddressOfHookSoundFunction, HookMainFunction);
|
The game work without issues like the others.
I have tried to hook 5/6 functions with some result.
at the first time I was think about a bug of my DLL but after do some search I have found this:
http://pro-software.it/hookfix.png
that confirm the game have a Anti-hooking EXE check with steamapi64.dll.
At this point without other alternatives I suppose the only way to follow is to patch the game exe.
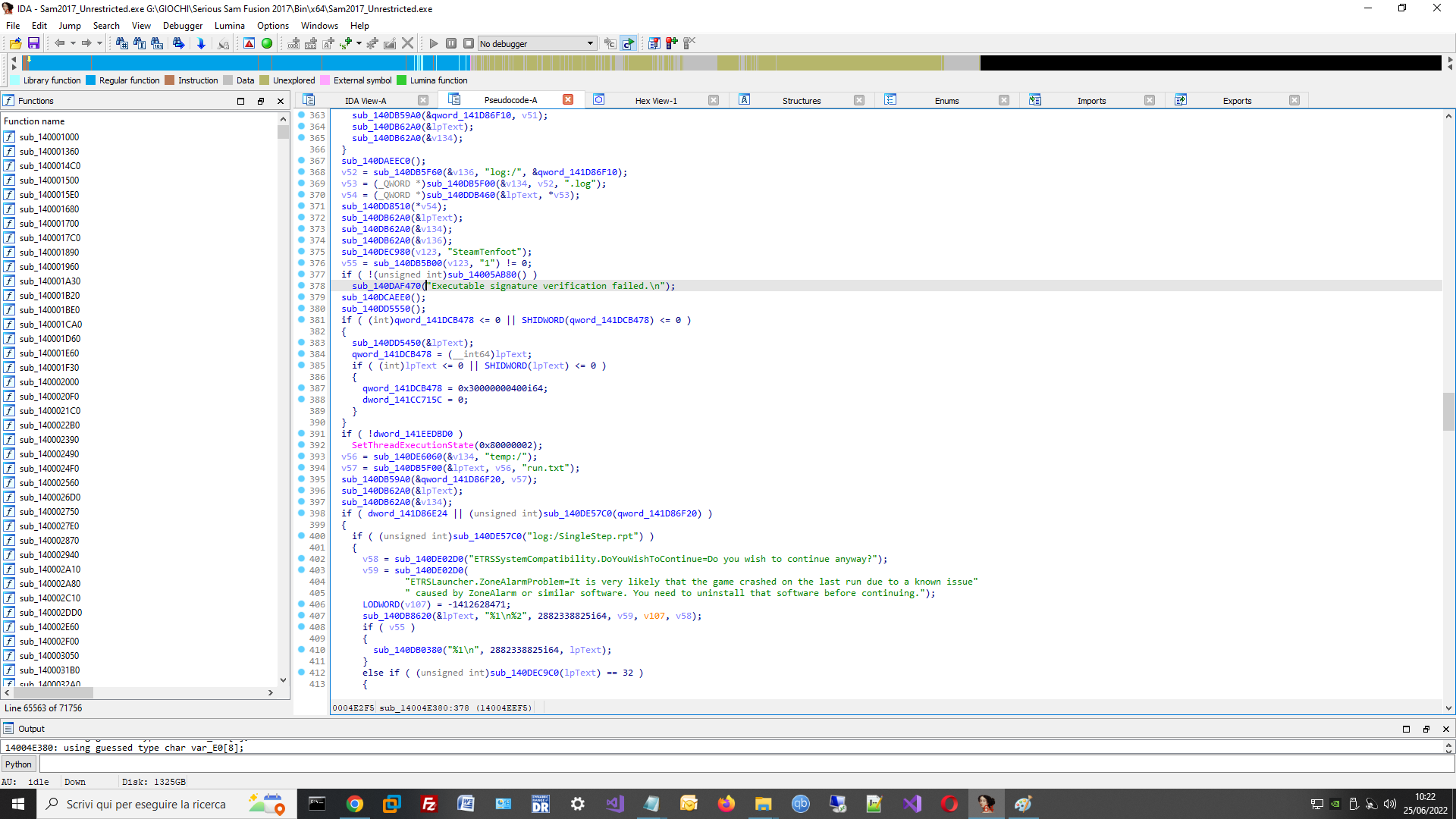
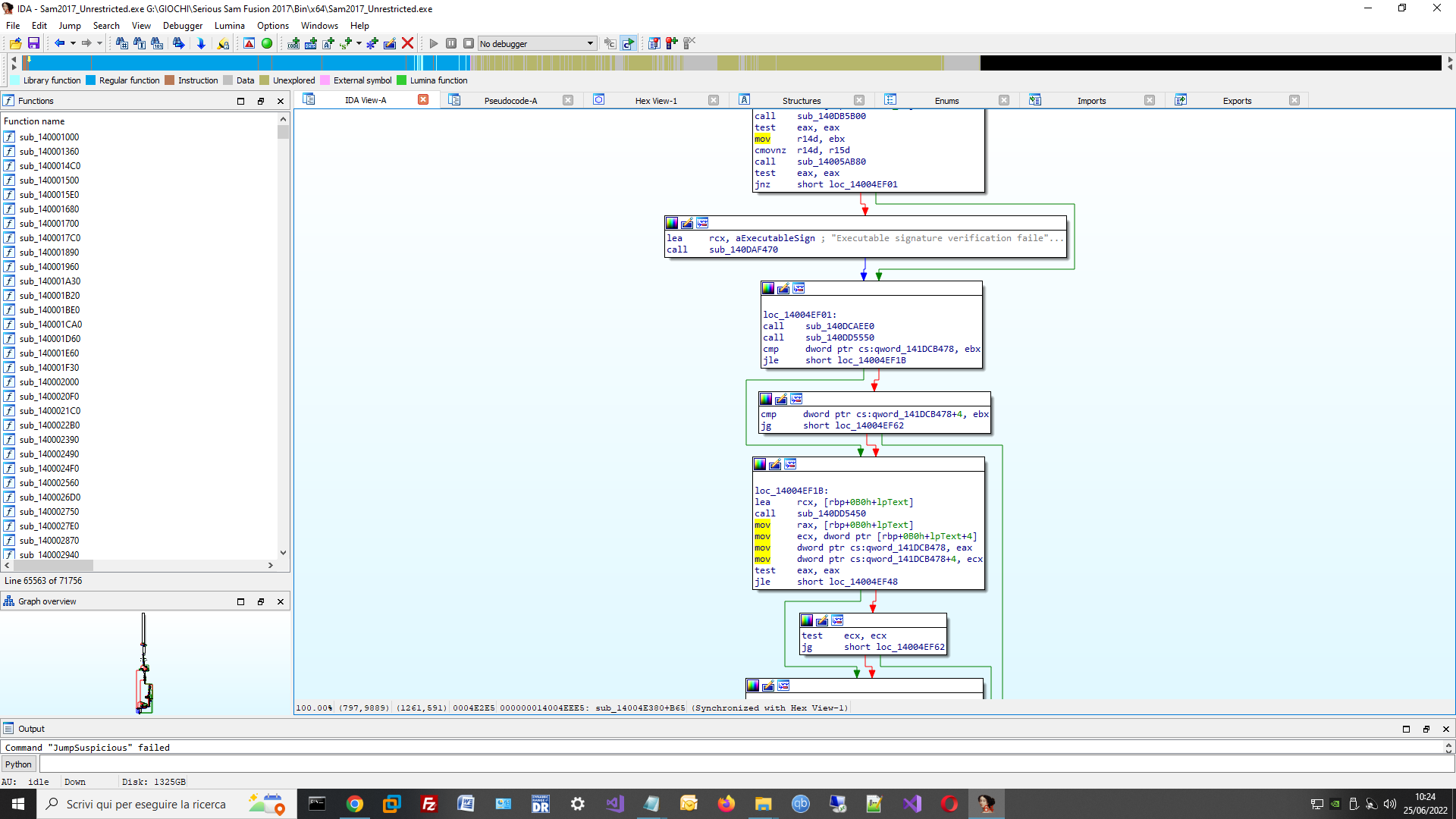
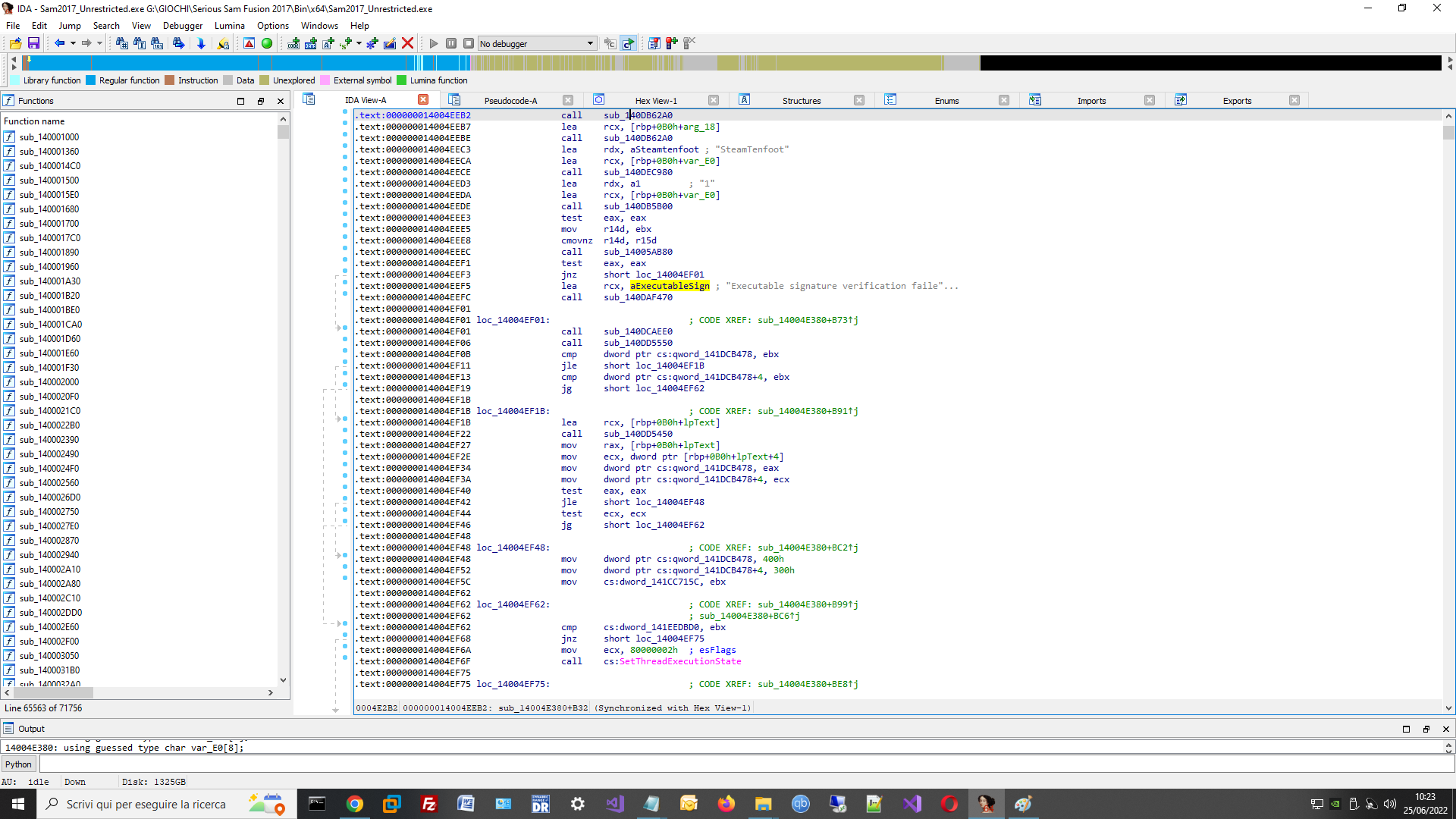
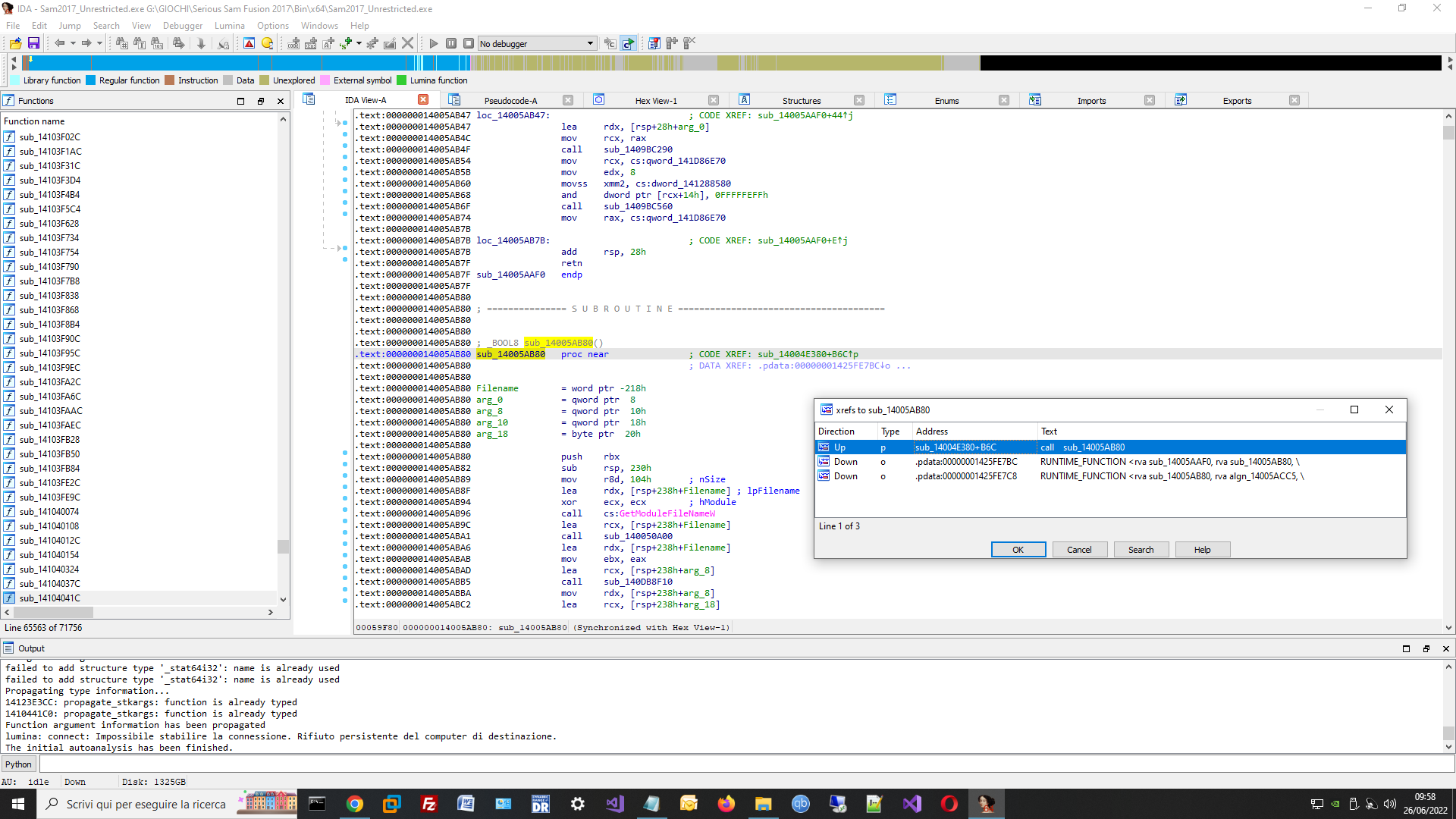
I attached the assembly code of IDA about this error message.
I don't have too much exeperiece in assembly, I have I already tried to patch the game but the game crash at startup.
Can you help me the patch this game ?
| Description: |
|
| Filesize: |
212.34 KB |
| Viewed: |
2387 Time(s) |
|
| Description: |
|
| Filesize: |
180.19 KB |
| Viewed: |
2390 Time(s) |
|
| Description: |
|
| Filesize: |
228.85 KB |
| Viewed: |
2389 Time(s) |
|
|
|
| Back to top |
|
 |
TsTg
Master Cheater
 Reputation: 5 Reputation: 5
Joined: 12 Dec 2012
Posts: 334
Location: Somewhere....
|
 Posted: Sat Jun 25, 2022 8:39 pm Post subject: Posted: Sat Jun 25, 2022 8:39 pm Post subject: |
 |
|
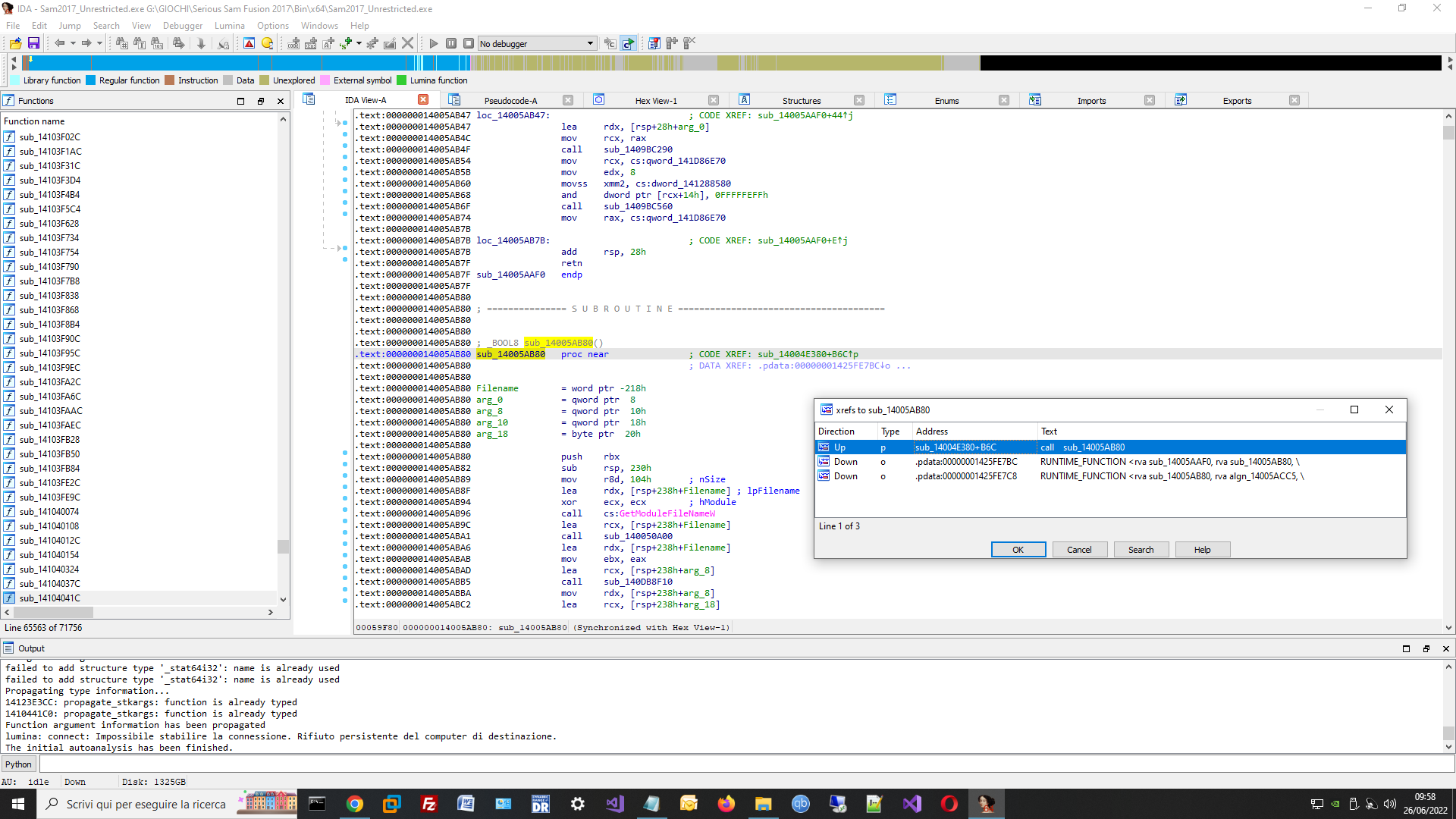
hmm so looking at the pictures, your point of intrest should be the function thats start at 14005AB80, but i can't tell does it expect a specific non-zero value or just anything (like a 1 for example), you can patch that from your dll's code (Using WriteProcessMemory API) or maybe in cheat engine or any other way.
you can try patching it to the following(address 14005AB80):
everytime that function is called, it returns one, evading that "verification failed" message.
[/code]
|
|
| Back to top |
|
 |
marco0999
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 28 Jun 2020
Posts: 29
Location: Italy
|
 Posted: Sun Jun 26, 2022 1:45 am Post subject: Posted: Sun Jun 26, 2022 1:45 am Post subject: |
 |
|
Thank you ! I have patched the exe with these modifications, but the game don't run here the code of function:
here the interest function:
| Code: |
.text:000000014005AB80 ; _BOOL8 sub_14005AB80()
.text:000000014005AB80 sub_14005AB80 proc near ; CODE XREF: sub_14004E380+B6C↑p
.text:000000014005AB80 ; DATA XREF: .pdata:00000001425FE7BC↓o ...
.text:000000014005AB80
.text:000000014005AB80 Filename = word ptr -218h
.text:000000014005AB80 arg_0 = qword ptr 8
.text:000000014005AB80 arg_8 = qword ptr 10h
.text:000000014005AB80 arg_10 = qword ptr 18h
.text:000000014005AB80 arg_18 = byte ptr 20h
.text:000000014005AB80
.text:000000014005AB80 push rbx
.text:000000014005AB82 sub rsp, 230h
.text:000000014005AB89 mov r8d, 104h ; nSize
.text:000000014005AB8F lea rdx, [rsp+238h+Filename] ; lpFilename
.text:000000014005AB94 xor ecx, ecx ; hModule
.text:000000014005AB96 call cs:GetModuleFileNameW
.text:000000014005AB9C lea rcx, [rsp+238h+Filename]
.text:000000014005ABA1 call sub_140050A00
.text:000000014005ABA6 lea rdx, [rsp+238h+Filename]
.text:000000014005ABAB mov ebx, eax
.text:000000014005ABAD lea rcx, [rsp+238h+arg_8]
.text:000000014005ABB5 call sub_140DB8F10
.text:000000014005ABBA mov rdx, [rsp+238h+arg_8]
.text:000000014005ABC2 lea rcx, [rsp+238h+arg_18]
.text:000000014005ABCA xor r8d, r8d
.text:000000014005ABCD call sub_140DDAF50
.text:000000014005ABD2 mov rdx, rax
.text:000000014005ABD5 lea rcx, [rsp+238h+arg_8]
.text:000000014005ABDD call sub_140DB59A0
.text:000000014005ABE2 lea rcx, [rsp+238h+arg_18]
.text:000000014005ABEA call sub_140DB62A0
.text:000000014005ABEF mov rdx, [rsp+238h+arg_8]
.text:000000014005ABF7 lea rcx, [rsp+238h+arg_18]
.text:000000014005ABFF call sub_140DB7440
.text:000000014005AC04 mov rdx, rax
.text:000000014005AC07 lea r8, aSteamApi64Dll ; "steam_api64.dll"
.text:000000014005AC0E lea rcx, [rsp+238h+arg_0]
.text:000000014005AC16 call sub_140DB5F00
.text:000000014005AC1B lea rcx, [rsp+238h+arg_18]
.text:000000014005AC23 call sub_140DB62A0
.text:000000014005AC28 mov rdx, [rsp+238h+arg_0]
.text:000000014005AC30 lea rcx, [rsp+238h+arg_18]
.text:000000014005AC38 call sub_140DDB460
.text:000000014005AC3D mov rdx, rax
.text:000000014005AC40 lea rcx, [rsp+238h+arg_0]
.text:000000014005AC48 call sub_140DB59A0
.text:000000014005AC4D lea rcx, [rsp+238h+arg_18]
.text:000000014005AC55 call sub_140DB62A0
.text:000000014005AC5A mov rdx, [rsp+238h+arg_0]
.text:000000014005AC62 lea rcx, [rsp+238h+arg_10]
.text:000000014005AC6A call sub_140DB90B0
.text:000000014005AC6F mov rcx, [rsp+238h+arg_10]
.text:000000014005AC77 call sub_140050A00
.text:000000014005AC7C test ebx, ebx
.text:000000014005AC7E jz short loc_14005AC8B
.text:000000014005AC80 test eax, eax
.text:000000014005AC82 jz short loc_14005AC8B
.text:000000014005AC84 mov ebx, 1
.text:000000014005AC89 jmp short loc_14005AC8D
.text:000000014005AC8B ; ---------------------------------------------------------------------------
.text:000000014005AC8B
.text:000000014005AC8B loc_14005AC8B: ; CODE XREF: sub_14005AB80+FE↑j
.text:000000014005AC8B ; sub_14005AB80+102↑j
.text:000000014005AC8B xor ebx, ebx
.text:000000014005AC8D
.text:000000014005AC8D loc_14005AC8D: ; CODE XREF: sub_14005AB80+109↑j
.text:000000014005AC8D shl cs:dword_141D4CD20, 1
.text:000000014005AC93 lea rcx, [rsp+238h+arg_10]
.text:000000014005AC9B call sub_140DB5830
.text:000000014005ACA0 lea rcx, [rsp+238h+arg_0]
.text:000000014005ACA8 call sub_140DB62A0
.text:000000014005ACAD lea rcx, [rsp+238h+arg_8]
.text:000000014005ACB5 call sub_140DB62A0
.text:000000014005ACBA mov eax, ebx
.text:000000014005ACBC add rsp, 230h
.text:000000014005ACC3 pop rbx
.text:000000014005ACC4 retn
.text:000000014005ACC4 sub_14005AB80 endp
.text:000000014005ACC4
.text:000000014005ACC4 ; ---------------------------------------------------------------------------
.text:000000014005ACC5 algn_14005ACC5: ; DATA XREF: .pdata:00000001425FE7C8↓o |
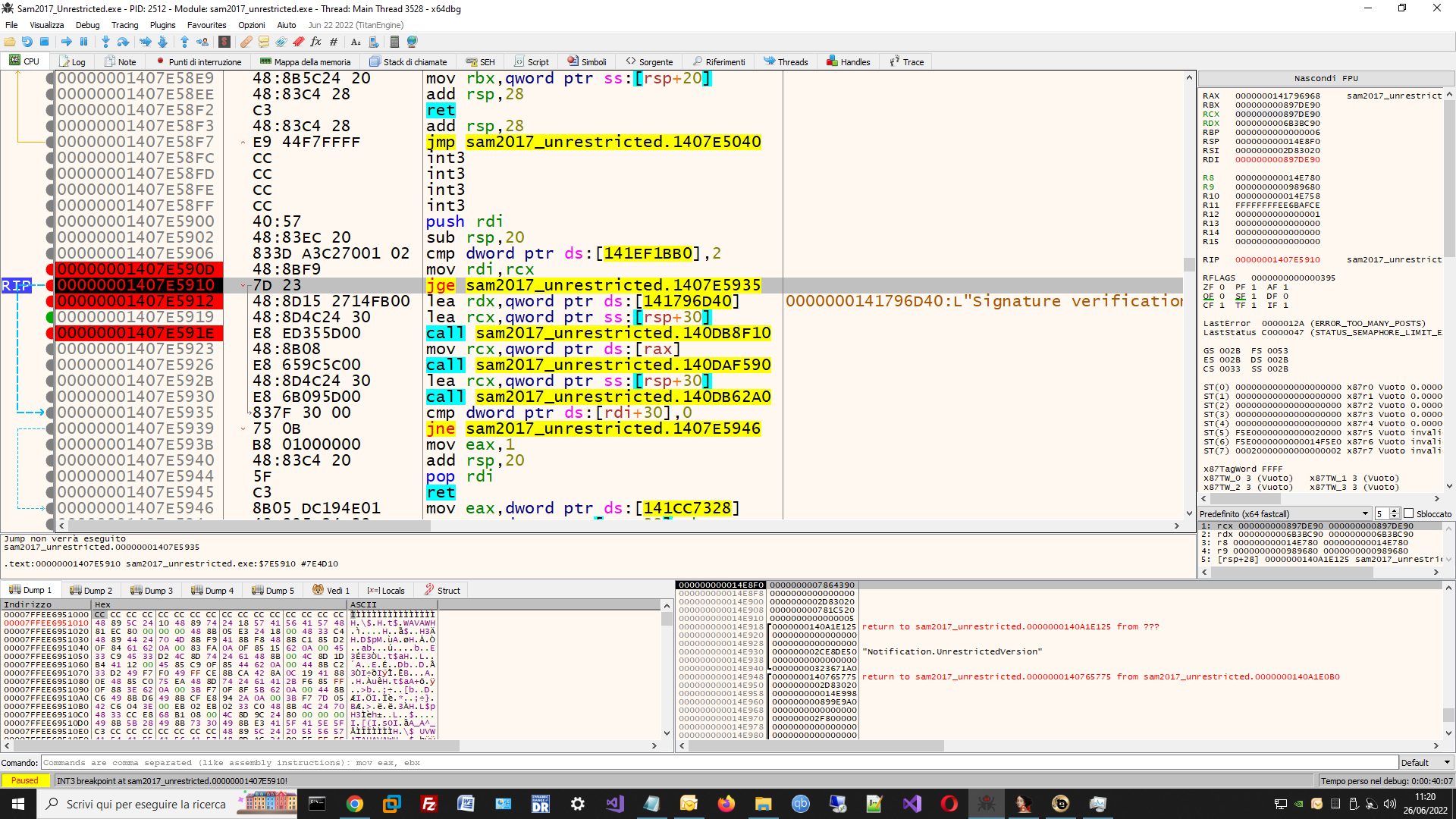
I have tested at debug and I confirm you that if I set 1 on eax the control is bypassed. but there is another control:
| Code: | .text:00000001407E5900 ; =============== S U B R O U T I N E =======================================
.text:00000001407E5900
.text:00000001407E5900
.text:00000001407E5900 sub_1407E5900 proc near ; CODE XREF: .text:00000001407E5350↑j
.text:00000001407E5900 ; sub_1407E5AF0+4↓p
.text:00000001407E5900 ; DATA XREF: ...
.text:00000001407E5900
.text:00000001407E5900 arg_0 = byte ptr 8
.text:00000001407E5900 arg_8 = qword ptr 10h
.text:00000001407E5900 arg_10 = qword ptr 18h
.text:00000001407E5900
.text:00000001407E5900 push rdi
.text:00000001407E5902 sub rsp, 20h
.text:00000001407E5906 cmp cs:dword_141EF1BB0, 2
.text:00000001407E590D mov rdi, rcx
.text:00000001407E5910 jge short loc_1407E5935
.text:00000001407E5912 lea rdx, aSignatureVerif ; "Signature verification of executable fa"...
.text:00000001407E5919 lea rcx, [rsp+28h+arg_0]
.text:00000001407E591E call sub_140DB8F10
.text:00000001407E5923 mov rcx, [rax]
.text:00000001407E5926 call sub_140DAF590
.text:00000001407E592B ; ---------------------------------------------------------------------------
.text:00000001407E592B lea rcx, [rsp+28h+arg_0]
.text:00000001407E6760 call sub_140DB62A0
.text:00000001407E5935
.text:00000001407E5935 loc_1407E5935: ; CODE XREF: sub_1407E5900+10↑j
.text:00000001407E5935 cmp dword ptr [rdi+30h], 0
.text:00000001407E5939 jnz short loc_1407E5946
.text:00000001407E593B mov eax, 1
.text:00000001407E6770 add rsp, 20h
.text:00000001407E5944 pop rdi
.text:00000001407E5945 retn
|
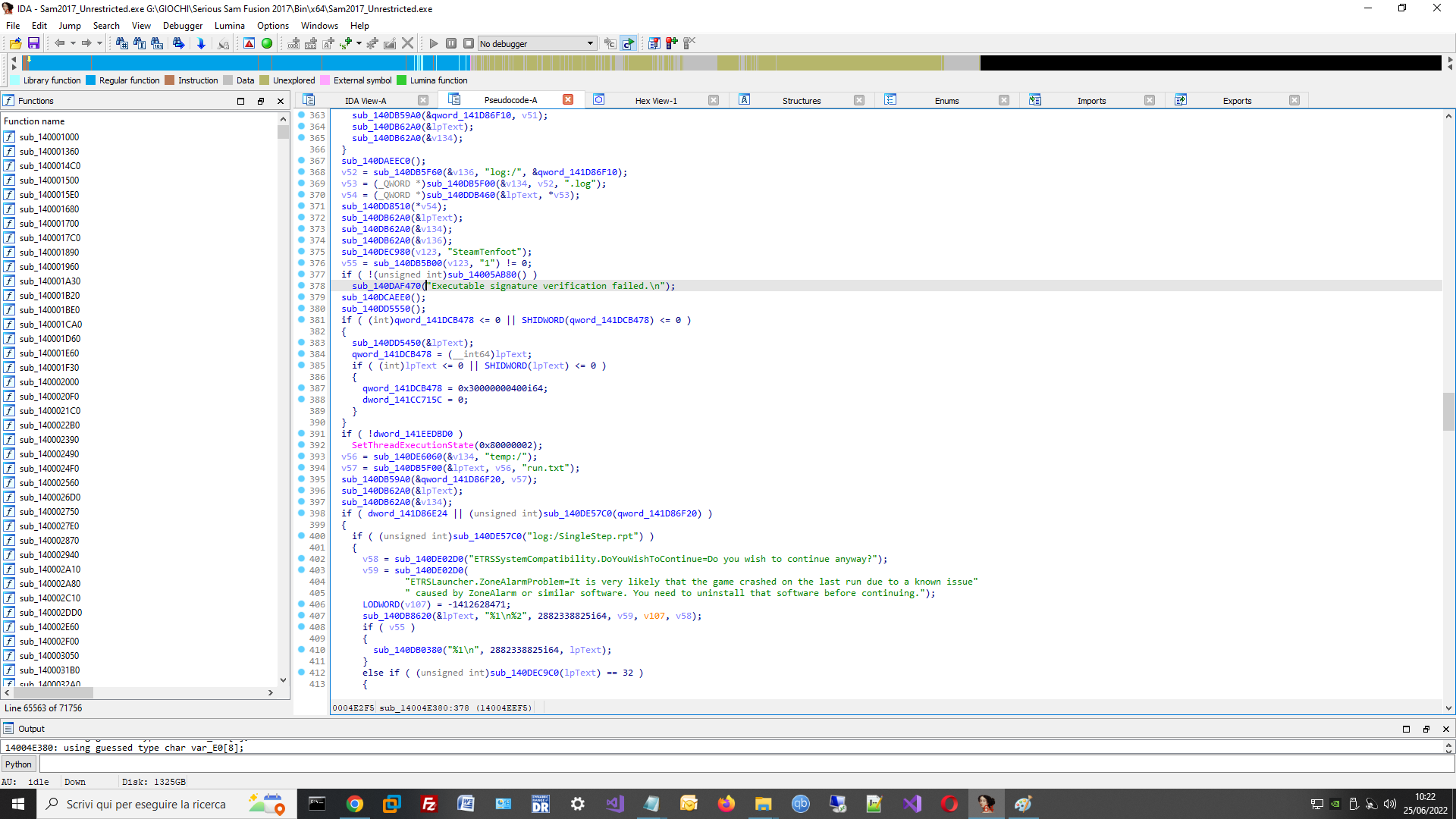
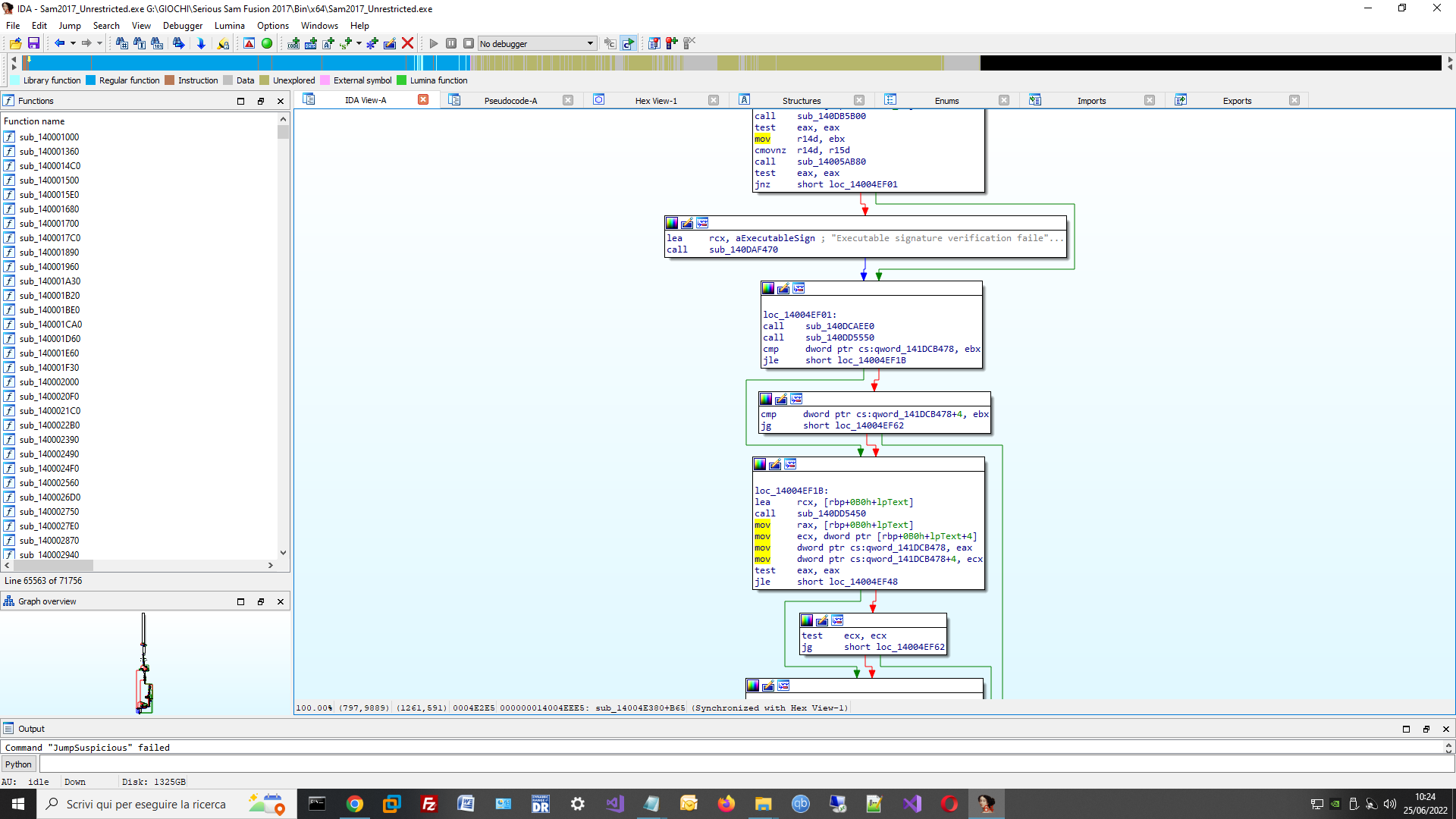
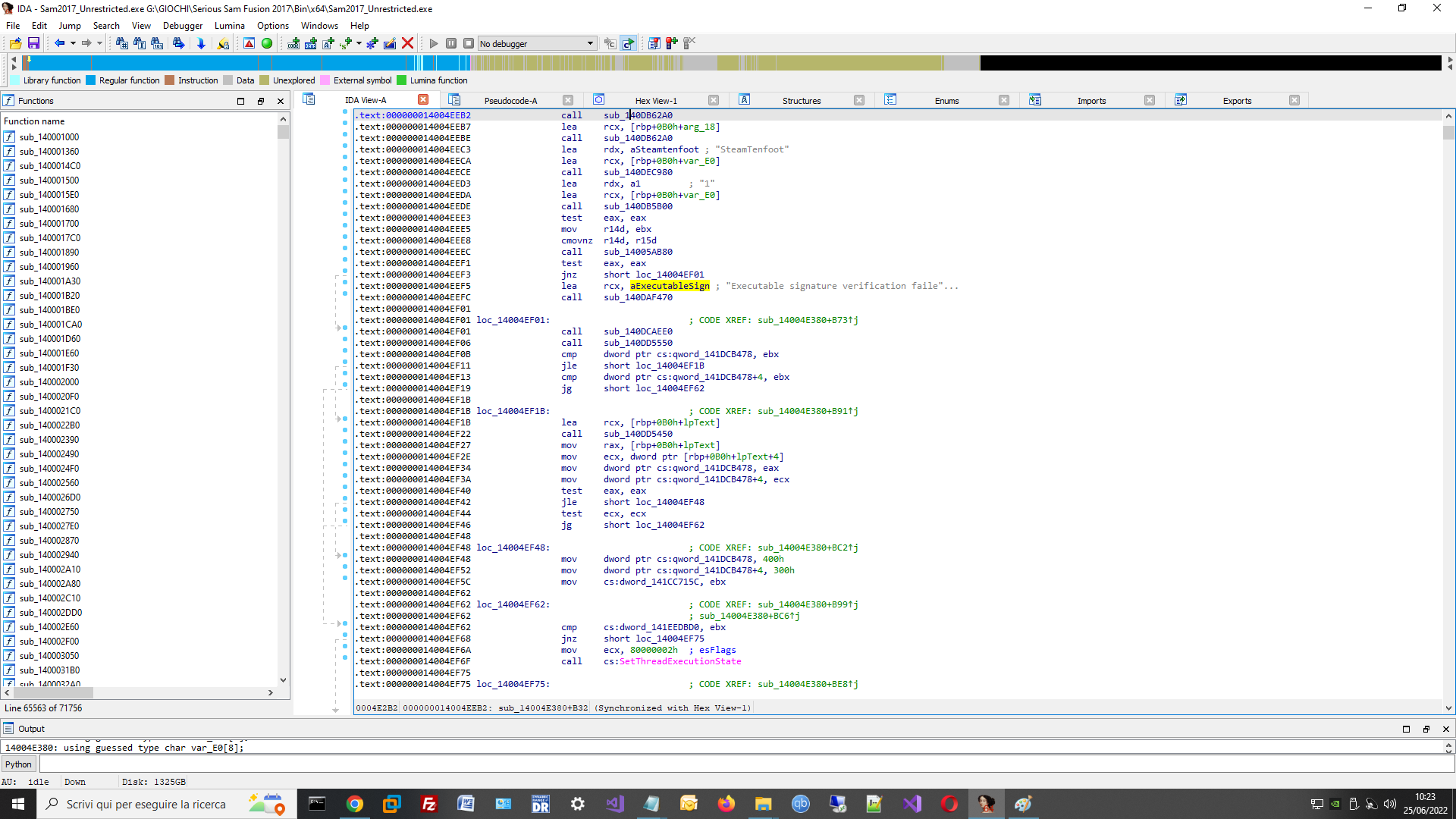
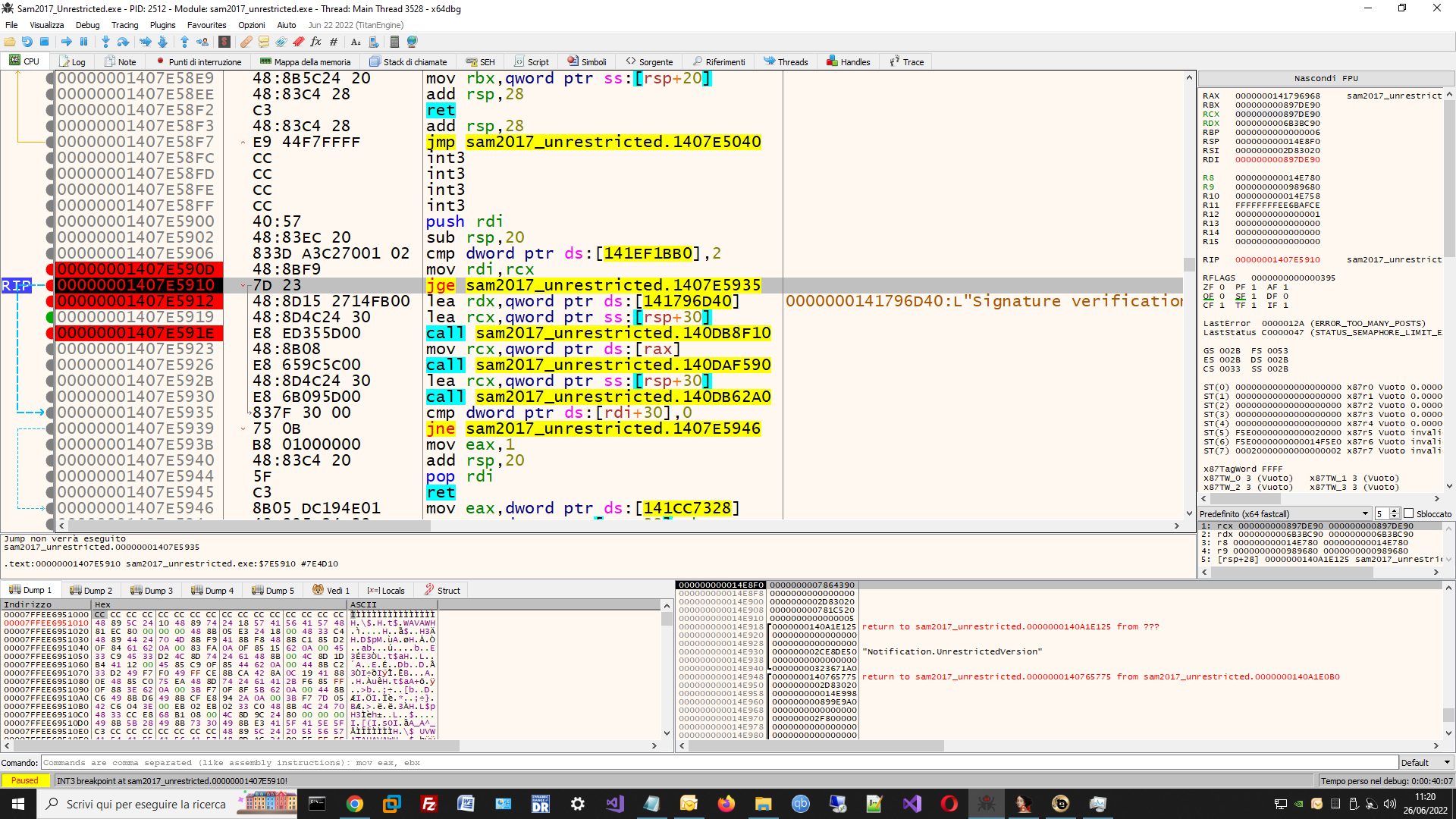
here the screenshot of debug:
probably is this second control that cause the error messagebox.
Update
The problem seem solved for the moment:
replaced:
.text:00000001407E5910 jge short loc_1407E5935
.text:00000001407E5912 lea rdx, aSignatureVerif ; "Signature
to
.text:00000001407E5910 jmp short loc_1407E5935
.text:00000001407E5912 lea rdx, aSignatureVerif ; "Signature
the game start normally with my hooked DLL without errors.
Hope the problem is really solved.
Thank you for all support !!
| Description: |
|
| Filesize: |
267.15 KB |
| Viewed: |
2316 Time(s) |
|
| Description: |
|
| Filesize: |
221.74 KB |
| Viewed: |
2321 Time(s) |
|
|
|
| Back to top |
|
 |
TsTg
Master Cheater
 Reputation: 5 Reputation: 5
Joined: 12 Dec 2012
Posts: 334
Location: Somewhere....
|
 Posted: Sun Jun 26, 2022 5:49 am Post subject: Posted: Sun Jun 26, 2022 5:49 am Post subject: |
 |
|
glad you have managed to solve the problem
basically the game is checking if the value at the address 141EF1BB0 is equal or bigger than 2, so you might want to set the value there (in case the game will do checks again during gameplay, etc) the patched jump simply bypassed the check and thus the game run.
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 5
Reputation: 5 Reputation: 5
Reputation: 5